Properties of RASP and its utilization
Applications have turned into a ready objective for hackers hoping to infiltrate the organization’s servers. There’s a valid justification for that. Hackers realize that if they can find and take advantage of a weakness in an application, they have greater chances of an effective information leakage. Also, the probability of tracking down a weakness in an application is great, as well. Experts say 90% of applications aren’t tested for weaknesses during their turn of events and quality assurance phases, and surprisingly more go unprotected during creation.
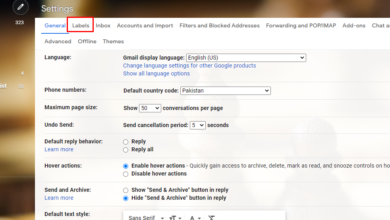
With so many powerless applications running in the endeavor, the test for network protectors is the means by which to shield those applications from assault. One way is to have the applications ensure themselves by recognizing and impeding assaults continuously. That is the thing that technology called Runtime Application Self Protection (RASP) does.
What is RASP?
RASP is a technology that works on a server level and kicks in when an application runs. It’s intended to distinguish assaults on an application continuously. At the point when an application starts to run, RASP can shield it from malevolent info or behavior by analyzing both the application’s work flow and the root of the behavior. By utilizing the application to persistently screen its own conduct, assaults can be recognized and relieved quickly without human mediation.
RASP fuses security into a running application any place it lives on a server. It blocks all calls from the application to a framework, ensuring they’re secure, and approves data requests directly inside the application. Both web and non-web applications can be ensured by RASP. The technology doesn’t influence the plan of the application since RASP’s recognition and assurance highlights work on the server the application’s running on.
How RASP functions?
At the point when a security issue in an application happens, RASP assumes responsibility for the application and addresses the issue. In indicative mode, RASP will simply send an alert that something is wrong. In security mode, it will attempt to stop it. For instance, it could stop the execution of files to a data base that seem, by all accounts, to be a SQL infusion assault.
Different functionalities that RASP incorporate are ending a user’s session, halting an application’s execution, or cautioning the user or security work force.
Designers can carry out RASP in two or three different ways. They can get to the technology through function calls written in an application’s source code, or they can take a built application and put it in a wrapper that permits the application to be secured with a solitary button push. The primary methodology is more exact on the grounds that engineers can settle on explicit choices regarding what they need ensured in the application, for example, logins, data set questions, and authoritative capacities.
Whichever technique is utilized with RASP, the outcome resembles packaging a web application firewall with the application’s runtime setting. That nearby association with the application implies RASP can be all the more finely tuned to the application’s security needs.
Read Also: Is Btech in Biotechnology a good career option for you?
Go past the edge for better application security
RASP imparts a few qualities to customary firewalls. For instance, it checks out traffic and content and can end meetings and sessions. In any case, firewalls are a border technology and can’t understand what’s happening inside the boundary. They don’t know the first thing what’s going on inside applications. What’s more, the border has become more permeable with the ascent of distributed computing and the expansion of cell phones. That has decreased the adequacy of both broadly useful firewalls and web application firewalls (WAFs).
Security advisors have an uncertain relationship with WAFs, in light of the fact that they are normally best the day they enter support and slowly become less powerful throughout the span of resulting months.
The justification behind this decrease in viability is that WAF arrangement frequently happens in light of some infiltration test or security occurrence after the association plays out an expense investigation and concludes a WAF organization is more affordable than fixing the application’s source code.”
Self-secured applications become a reality
A benefit of RASP is it can secure a framework once a hacker has entered perimeter guards. It has knowledge into application rationale, arrangement, and data flows. That implies RASP can foil assaults with high exactness. It can recognize real assaults and genuine solicitations for data, which lessens false positives and permits network administrators to invest a greater amount of their energy fighting genuine issues and less time pursuing computerized security problems.
Furthermore, its capacity to self-secure an application’s information implies security goes with the information from its start till the end. That can be especially valuable to associations that need to meet consistence necessities, since self-secured information is futile to information leakages. Now and again, controllers don’t need reporting an information leak assuming the leaked information is encrypted or in a structure that makes it unreadable whenever used.
Likewise with WAFs, RASP won’t fix an application’s source code itself. Nonetheless, experts clarified that it coordinates with an application’s hidden code libraries and secures the weak spaces of the application at the source level.
At the point when a client settles on a function call containing parameters that may damage the web application. RASP catches the call at runtime, logging or hindering the call, contingent upon the design. This technique for shielding a web application contrasts on a very basic level from a WAF.
Better technology for devices, however at a cost
RASP can likewise help mobile devices. Contingent upon mobile working frameworks, shielding applications from assaults is a questionable suggestion for associations. Securing them with RASP can make devices to a low security challenge for an IT office.
On the disadvantage, application performance can fail when RASP is deployed, although the amount of a failure is unjustified among experts and masters of the technology. The self securing feature can slow down an application, as can the unique idea of RASP. Assuming that inactivity becomes clear to users, it will unquestionably create grousing inside an association. Nonetheless, how high the performance issue is will not be clear until more applications begin using RASP into their capacities. For more information regarding RASP and other features, visit Appsealing at the website available online.